Robotic Process Automation Industry
The robotic process automation (RPA) industry has rapidly emerged as a transformative force across multiple sectors, enabling businesses to automate repetitive, rule-based tasks using software robots. These digital workers mimic human actions to interact with systems, input data, trigger responses, and streamline workflows — all without human intervention. As organizations seek higher efficiency, lower operational costs, and improved accuracy, RPA has become a strategic tool for digital transformation. What Is Robotic Process Automation? Robotic Process Automation is a software-based technology that uses bots or “robots” to automate high-volume, repetitive tasks that typically require human input. RPA robots can work across applications, perform rule-driven operations, and integrate seamlessly with legacy systems — without requiring backend changes or APIs. This makes RPA highly accessible, fast to deploy, and scalable across enterprises. How the RPA Industry Works The RPA industry consists of software vendors, service providers, system integrators, and enterprises leveraging automation solutions. Vendors develop RPA platforms and tools, while service providers help organizations implement and maintain these systems. The industry is driven by growing demand for digital efficiency and cost optimization. Core Features of RPA Software Modern RPA platforms offer a wide range of functionalities to automate diverse workflows across business units: Visual Workflow Design: Drag-and-drop interfaces for building automation sequences without coding. Screen Scraping: Extracts data from web applications, legacy systems, and GUIs. Rule-Based Logic: Automates tasks that follow consistent, defined rules or decision trees. Data Entry Automation: Inputs, updates, and validates data across multiple systems. Integration with AI/ML: Enhances bots with cognitive capabilities like NLP, OCR, and sentiment analysis. Bot Scheduling and Orchestration: Centrally manages bot deployment, load balancing, and execution logs. Applications of RPA in Industry While RPA originated in business process automation, its applications now span both corporate functions and industrial operations: Manufacturing Automates supply chain workflows, inventory tracking, quality reporting, and production scheduling by integrating ERP systems and MES platforms. Finance and Accounting Handles invoice processing, reconciliations, financial reporting, and compliance monitoring with speed and accuracy. Healthcare Manages patient data entry, appointment scheduling, insurance claim validation, and regulatory reporting. Human Resources Automates onboarding, payroll, employee data updates, and compliance document management. Customer Service Supports ticket routing, data entry, and resolution tracking by working alongside chatbots and CRMs. Benefits of RPA for Organizations Businesses across the world are adopting RPA for its measurable impact on productivity, cost, and agility: Increased Efficiency: Bots work 24/7 without breaks, speeding up task execution. Cost Reduction: Automating tasks significantly lowers labor costs and resource usage. Error Elimination: RPA eliminates manual entry errors and ensures consistent task performance. Scalability: Enterprises can deploy hundreds of bots to scale operations as demand grows. Compliance: Automation creates audit trails and ensures standardized documentation. RPA and Industry 4.0 The RPA industry is playing a vital role in the broader digital transformation driven by Industry 4.0. While traditional RPA focused on business processes, industrial automation is merging RPA with technologies like: Artificial Intelligence Combining RPA with AI unlocks intelligent automation — enabling bots to learn, make decisions, and adapt over time. Internet of Things (IoT) RPA systems can act on real-time IoT sensor data, triggering maintenance tasks or alerts automatically. Edge Computing Edge-based RPA systems process data locally at the source, enabling faster decisions in remote or time-sensitive operations. Digital Twins Simulated environments use RPA to test and optimize workflows virtually before deploying them on the production floor. Challenges in the RPA Industry Despite its rapid growth, the RPA industry faces a number of implementation and scalability challenges: Process Selection: Not all tasks are suitable for RPA; selecting the right use cases is critical. Bot Maintenance: System or UI changes may break bots, requiring ongoing monitoring and updates. Security: Bots may handle sensitive data and require strict access control and logging. Integration with Legacy Systems: RPA often depends on surface-level integrations, which can be fragile. Employee Resistance: Workforce concerns around job displacement may hinder adoption. Leading RPA Platforms The RPA software market includes several well-established and emerging players offering powerful automation platforms: UiPath: Known for ease of use, AI integrations, and enterprise-grade scalability. Automation Anywhere: Offers cloud-native RPA with advanced analytics and bot store features. Blue Prism: Focuses on secure, scalable digital workforce solutions for large organizations. Microsoft Power Automate: Integrates natively with the Microsoft ecosystem and Office tools. NICE: Provides attended and unattended bots tailored for contact centers and customer service. The Future of the RPA Industry The robotic process automation industry is shifting toward hyperautomation — the convergence of RPA, AI, ML, and process mining. Future RPA systems will be more autonomous, self-healing, and capable of continuous improvement through AI-driven insights. Industry analysts predict the growing use of RPA in manufacturing, logistics, defense, healthcare, and beyond — solidifying its place in the next era of industrial automation.
Defense Communication Systems Software

Defense communication systems software plays a mission-critical role in modern military operations by enabling secure, reliable, and interoperable communications across land, air, sea, space, and cyber domains. These software platforms are designed to support real-time data exchange, encrypted voice and video transmission, tactical messaging, and command-and-control communications under the most demanding conditions. What Is Defense Communication Systems Software? Defense communication systems software refers to specialized platforms that manage, control, and secure military communications across a variety of technologies and protocols. These systems ensure that military personnel, command centers, and allied forces can communicate effectively, regardless of location or operational environment. The software supports voice, video, and data transmissions over secure and resilient networks. Key Features and Capabilities Modern defense communication software is designed to meet the rigorous demands of battlefield communications, often in denied, degraded, or disrupted environments. Common features include: End-to-End Encryption: Secure communications with AES, ECC, or other military-grade encryption standards. Interoperability: Supports NATO and coalition protocols to enable joint operations across different systems. Multi-Channel Communication: Simultaneous handling of voice, data, video, and telemetry over various media. Redundancy and Failover: Automatic switching between communication paths to maintain uptime. Software-Defined Radios (SDR) Integration: Seamless control of frequency hopping and waveform selection. Network Management: Monitoring and configuring networks in real-time, including bandwidth, QoS, and security. Applications in Military Operations Defense communication software is deployed across all levels of operations, from individual warfighters to strategic command centers: Tactical Edge Communication Used by soldiers and field units for mission-critical voice and data transmission. The software must support mobile ad hoc networks (MANETs), GPS synchronization, and fast device pairing in dynamic environments. Command and Control (C2) Systems These systems rely on secure and structured communication protocols to issue commands, receive situational updates, and manage battlefield assets. C2 software integrates with ISR (Intelligence, Surveillance, Reconnaissance) and fire control systems. Naval and Aerospace Communication Aircraft, ships, and unmanned systems require communication software that works across satellite links, line-of-sight (LOS), and beyond-line-of-sight (BLOS) networks. Redundancy, encryption, and real-time video streaming are critical. Cybersecurity Command Platforms Defense communication software also supports cyber operations by providing secure messaging, real-time alerts, and integration with cyber situational awareness tools and SOCs (Security Operations Centers). Integration with Modern Defense Technologies For optimal effectiveness, defense communication systems software integrates with a wide range of modern military technologies: Software-Defined Radios (SDRs) SDRs rely on flexible software platforms to change frequencies, modulations, and waveforms on-the-fly, enabling communication in contested electromagnetic environments. Battle Management Systems (BMS) Communication software connects BMS platforms to share situational awareness, coordinate operations, and track friendly and enemy positions in real time. Satellite Communication (SATCOM) Defense software supports uplink/downlink management, beamforming, and bandwidth control for SATCOM systems, especially in remote or mobile theaters of operation. Unmanned Systems (UxVs) Communication with drones, unmanned ground vehicles (UGVs), and autonomous maritime systems requires low-latency, secure links managed by advanced communication software. Standards and Protocols in Defense Communication Compliance with international and defense-specific standards ensures secure and interoperable communication. Common standards include: NATO STANAGs: Standardization Agreements for secure tactical communication between allied forces. MIL-STD-188: U.S. military standards for interoperability and secure communications. IP-based Protocols: Including IPv6, VoIP, and multicast communication for scalability and flexibility. JREAP and Link 16: Tactical data link protocols for sharing real-time battlefield data across platforms. Security Considerations Defense communications software must provide multi-layered security to protect against cyber espionage, jamming, and spoofing: Secure Key Management: Automated generation, distribution, and revocation of encryption keys. Role-Based Access Control: Restricts communication access based on rank, mission, or clearance level. Intrusion Detection: Software detects and alerts operators of suspicious behavior or communication anomalies. Frequency Agility: Supports frequency hopping and anti-jamming techniques for resilient connectivity. Benefits of Advanced Communication Software Deploying advanced communication systems software provides numerous advantages for defense forces: Operational Continuity: Maintains connectivity even in hostile or remote environments. Faster Decision-Making: Real-time data transmission supports rapid situational awareness and command execution. Force Coordination: Enables joint missions, synchronized maneuvers, and information sharing across units and nations. Scalability: From single-device communication to large-scale theater operations, software can scale accordingly. Cost Efficiency: Software-defined systems reduce reliance on hardware upgrades and simplify maintenance. Future Trends in Military Communication Software Defense communication software is rapidly evolving with advancements in AI, 5G, and secure mesh networking. Emerging trends include: AI-Assisted Communication Management Artificial intelligence helps prioritize traffic, detect threats, and optimize bandwidth in real time, especially under high-load conditions. 5G and Beyond Fifth-generation networks provide ultra-low latency, high-speed connectivity for urban and tactical deployments, enabling real-time ISR and unmanned operations. Quantum-Resistant Encryption Next-generation cryptography is being developed to protect defense communication systems from future quantum computing threats. Edge-Based Communication Nodes Deploying communication capabilities closer to the battlefield with edge computing ensures faster responses and improved fault tolerance. Multi-Domain Integration Seamless communication across cyber, space, air, land, and sea domains will be the foundation of next-generation joint-force operations.
Industrial Data Acquisition Software

Industrial data acquisition software is a critical component in the digital transformation of manufacturing and process industries. By capturing and analyzing real-time data from machinery, sensors, and control systems, these software platforms help organizations monitor operations, detect anomalies, ensure safety, and optimize productivity. As Industry 4.0 continues to advance, robust data acquisition systems have become essential for smart factories and automated environments. What Is Industrial Data Acquisition Software? Industrial data acquisition software (DAQ) refers to digital platforms that collect, record, process, and visualize signals from various sensors and industrial devices. It connects hardware systems—like PLCs, RTUs, and embedded controllers—to software environments that interpret and use the data for real-time decision-making, control, or historical analysis. Key Components of Data Acquisition Systems An effective industrial DAQ system typically includes the following components: Sensors and Transducers: Devices that convert physical parameters (temperature, pressure, flow, etc.) into electrical signals. DAQ Hardware: Interfaces such as data loggers, I/O modules, and signal conditioners that connect sensors to computing systems. DAQ Software: The application responsible for acquiring, processing, storing, and displaying data from connected sources. Communication Protocols: Standards such as Modbus, OPC UA, and MQTT that ensure reliable data transmission. Main Functions of Industrial DAQ Software Modern DAQ software offers a variety of features to enhance data management and operational efficiency: Real-Time Monitoring: Live data streaming from sensors and devices to dashboards for immediate visibility. Data Logging: Continuous or event-based recording of historical data for compliance, diagnostics, or analysis. Alarm Management: Triggering alerts based on threshold violations or unexpected system behaviors. Data Visualization: Custom dashboards, trends, charts, and heatmaps for intuitive analysis. Edge Processing: Local data analysis before sending to cloud or SCADA systems, reducing latency and bandwidth usage. Remote Access: Secure web or mobile interfaces to monitor systems from any location. Use Cases Across Industries Industrial data acquisition software is deployed in various sectors to improve transparency, compliance, and efficiency: Manufacturing: Machine monitoring, performance analytics, and predictive maintenance. Oil & Gas: Pipeline monitoring, flow measurement, and safety system validation. Utilities: Power grid monitoring, substation data collection, and demand forecasting. Pharmaceutical: Environmental condition logging and compliance with regulatory standards like FDA 21 CFR Part 11. Food & Beverage: Temperature and humidity tracking during production and storage. Integration with Industrial Systems DAQ software must seamlessly integrate with existing industrial automation infrastructure. Key integration points include: PLCs and RTUs Programmable logic controllers and remote terminal units are commonly used to relay data from field devices. DAQ software must be compatible with various PLC brands and support high-speed communication protocols. SCADA Systems Supervisory Control and Data Acquisition (SCADA) platforms often use DAQ software to collect field-level data for higher-level visualization and control operations. Industrial IoT Platforms Cloud-based IIoT platforms aggregate data from multiple locations. DAQ software supports this ecosystem by providing clean, structured, and secure data for cloud analytics. Benefits of Industrial Data Acquisition Software Organizations using robust DAQ systems gain multiple advantages across their operations: Improved Operational Visibility: Real-time insights into system performance, asset conditions, and process variables. Enhanced Productivity: Data-driven optimization reduces bottlenecks, waste, and downtime. Predictive Maintenance: Early detection of anomalies helps avoid unplanned outages and extend equipment life. Compliance and Reporting: Automated data logging ensures adherence to industry and regulatory standards. Informed Decision-Making: Historical and live data support more accurate planning and troubleshooting. Key Features to Look For When selecting industrial DAQ software, manufacturers should evaluate the following capabilities: Scalability: Ability to expand as sensor networks and facilities grow. Multi-Protocol Support: Compatibility with various industrial communication standards. User-Friendly Interface: Intuitive configuration and dashboard design tools. Security: Data encryption, access control, and secure data transmission. Custom Analytics: Built-in or third-party integrations for advanced data modeling and AI-based insights. Emerging Trends in Data Acquisition The future of industrial data acquisition is shaped by emerging technologies and changing operational needs. Current trends include: Edge Analytics Processing data near the source enables faster responses, reduces cloud dependency, and improves reliability in remote environments. AI-Powered Diagnostics Machine learning algorithms analyze patterns in sensor data to detect early warning signs and optimize system performance. Cloud-Native Architectures Modern DAQ solutions offer cloud-based deployment, enabling centralized management, remote updates, and seamless scalability. Digital Twins By combining real-time data with digital models, digital twins simulate processes and assets for deeper insights and scenario planning. Open Source and API-Driven Platforms Open architecture allows manufacturers to build flexible, vendor-neutral systems that adapt to unique operational requirements.
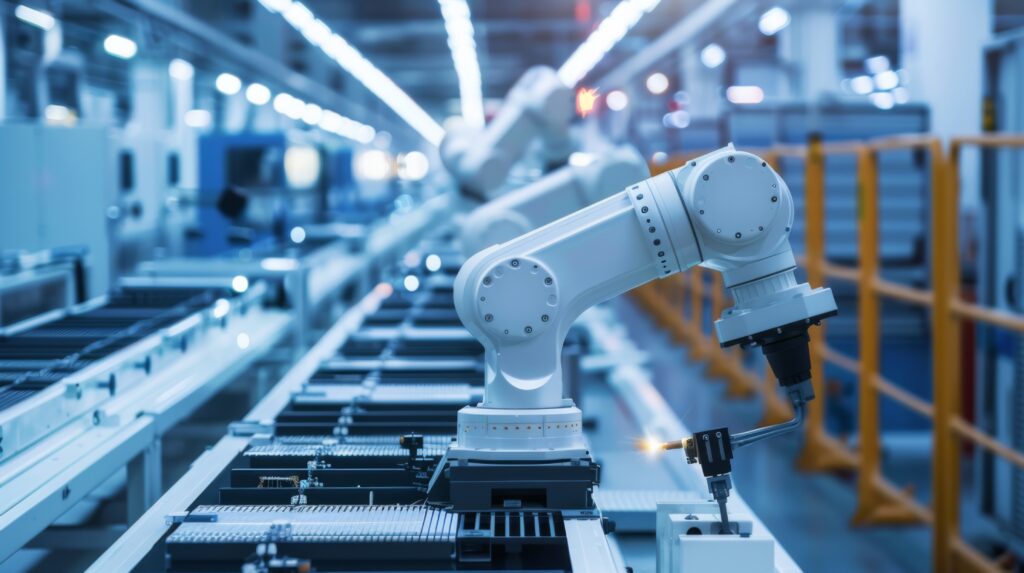
Automated Manufacturing Software

Automated manufacturing software is revolutionizing the way modern factories operate by integrating intelligent control systems, data analytics, and process automation into a single, scalable solution. These platforms allow manufacturers to optimize production efficiency, reduce human error, increase output quality, and gain real-time visibility across the entire factory floor. What Is Automated Manufacturing Software? Automated manufacturing software refers to digital platforms that manage, control, and optimize production processes without the need for continuous human intervention. It includes modules for scheduling, machine control, quality assurance, predictive maintenance, and real-time analytics. By integrating machinery, sensors, and enterprise systems, these solutions enable smart and autonomous manufacturing operations. Core Functions and Capabilities Modern automated manufacturing platforms offer a wide range of functionalities tailored to different manufacturing needs. Common features include: Production Scheduling: Automatically allocates tasks based on resource availability, order priority, and machine capacity. Machine Control Integration: Interfaces directly with PLCs, CNCs, and robots to coordinate real-time machine operations. Quality Monitoring: Tracks defects and process deviations using statistical process control (SPC) tools. Predictive Maintenance: Uses data from sensors and IoT devices to forecast equipment failures before they occur. Energy Management: Monitors power usage and identifies inefficiencies in real-time. Traceability: Tracks raw materials, components, and final products throughout the entire production cycle. Types of Automated Manufacturing Software Different types of software solutions support automation in various aspects of manufacturing. These include: Manufacturing Execution Systems (MES) MES software provides a real-time interface between the shop floor and business systems like ERP. It manages production orders, workforce assignments, and material usage. Supervisory Control and Data Acquisition (SCADA) SCADA systems collect and visualize data from sensors and machines, allowing operators to monitor and control operations across distributed sites. Industrial Internet of Things (IIoT) Platforms IIoT software connects machines and sensors to the cloud, enabling real-time data collection, remote monitoring, and AI-powered insights. Computer-Aided Manufacturing (CAM) CAM software automates the planning, control, and optimization of manufacturing processes, especially in machining and toolpath generation. Benefits of Automated Manufacturing Software Implementing automated software in a manufacturing environment yields significant operational and strategic benefits: Increased Efficiency: Reduces downtime, accelerates throughput, and minimizes manual intervention. Enhanced Product Quality: Consistent process execution reduces variability and defects. Lower Operational Costs: Optimizes labor, energy, and material usage. Scalability: Easily adapts to production expansion or the introduction of new product lines. Data-Driven Decision Making: Real-time analytics and dashboards support faster, smarter decisions. Industry Applications Automated manufacturing software is utilized across various sectors, each with specific automation needs and requirements: Automotive: Assembly line automation, robotic welding, and vision-based quality inspection. Electronics: Precision assembly, SMT line control, and real-time yield monitoring. Pharmaceuticals: Batch control, compliance monitoring, and digital documentation. Food & Beverage: Recipe management, hygienic process control, and traceability. Textiles: Automated dyeing, weaving, and defect detection systems. Integration With Other Industrial Systems Effective automated manufacturing relies on seamless integration with various operational and enterprise systems: ERP Integration By linking with ERP systems, manufacturing software ensures synchronization between production and business operations like inventory, finance, and procurement. SCADA and HMI Integration with SCADA and HMI platforms allows real-time process control and operator interaction, enhancing transparency and responsiveness on the factory floor. PLCs and CNCs Direct communication with PLCs and CNC machines ensures precise control over production equipment and automation workflows. Emerging Trends in Automated Manufacturing As technology advances, automated manufacturing software is evolving rapidly to support more intelligent, flexible, and connected production systems. AI and Machine Learning AI algorithms are increasingly used for process optimization, defect prediction, and autonomous quality control. Digital Twins Virtual replicas of physical production systems enable real-time simulation, predictive analytics, and optimization before changes are made on the factory floor. 5G and Edge Computing 5G networks and edge computing provide ultra-fast data transmission and low latency for distributed control and real-time decision-making at the machine level. Sustainability and Green Manufacturing Modern automation platforms include tools for monitoring carbon emissions, reducing energy consumption, and promoting sustainable practices in manufacturing.
Defense Cybersecurity Solutions

Defense cybersecurity solutions are at the forefront of modern military operations, protecting critical assets from digital threats, espionage, sabotage, and cyber warfare. As military systems become increasingly connected and reliant on digital infrastructure, the need for robust, multi-layered cybersecurity has never been greater. From securing battlefield communication to protecting classified data, cybersecurity is a strategic pillar in national defense. What Are Defense Cybersecurity Solutions? Defense cybersecurity solutions refer to the technologies, frameworks, and practices used to safeguard military IT systems, operational networks, weapons platforms, and digital assets from cyber attacks. These solutions include everything from endpoint protection and network monitoring to encrypted communications and zero-trust architectures. Their primary goal is to ensure mission continuity, data integrity, and operational security in the face of constantly evolving threats. Why Cybersecurity Is Critical in Defense Cyber threats in the defense sector are increasingly sophisticated, often state-sponsored, and capable of causing severe disruption or intelligence compromise. These threats can target: Command and control systems Weapon systems and embedded platforms Communication networks Supply chains and logistics software Military satellites and space assets Failing to protect these systems can result in operational paralysis, mission failure, or unauthorized access to critical national intelligence. Core Components of Defense Cybersecurity Modern cybersecurity solutions for defense rely on a layered defense approach. Key components include: Network Security and Monitoring Firewalls, intrusion detection/prevention systems (IDS/IPS), and security information and event management (SIEM) tools monitor traffic and detect suspicious activity across military networks in real time. Endpoint Protection All devices, from laptops to drones and embedded control systems, are secured with endpoint detection and response (EDR) technologies that monitor for anomalies and execute automatic countermeasures. Encryption and Secure Communications End-to-end encryption ensures the confidentiality of communications between command centers, field units, and coalition partners. Military-grade cryptography is used to prevent data interception and tampering. Identity and Access Management (IAM) Strict authentication, role-based access, and zero-trust policies control who has access to what systems, minimizing the risk of insider threats or unauthorized access. Cyber Threat Intelligence (CTI) Cyber threat intelligence platforms gather, analyze, and share information about emerging threats, attacker behaviors, and vulnerabilities to anticipate and prevent attacks proactively. Common Threats in Military Cyber Domains Defense systems face a unique set of cyber threats due to their complexity and geopolitical significance. These threats include: Advanced Persistent Threats (APTs): Long-term, targeted attacks often conducted by nation-states. Ransomware: Disrupts mission-critical systems and demands payment to restore access. Supply Chain Attacks: Exploiting third-party software or hardware components to infiltrate defense systems. Insider Threats: Malicious or negligent actors within defense organizations. Zero-Day Exploits: Attacks targeting previously unknown software vulnerabilities. Cybersecurity for Tactical and Embedded Systems Military vehicles, drones, aircraft, and weapon systems increasingly rely on embedded software and network connectivity. These platforms require real-time protection that is lightweight, resilient, and often autonomous. Specialized cybersecurity solutions are integrated directly into embedded systems to provide: Secure boot and firmware integrity Runtime memory protection Secure data storage Over-the-air (OTA) secure updates Cyber Defense Operations and SOCs Security Operations Centers (SOCs) within defense organizations monitor, detect, analyze, and respond to cyber threats 24/7. These centers are equipped with advanced tools like: AI-powered threat detection Behavioral analytics Automated incident response Forensic analysis systems In military contexts, SOCs also work closely with intelligence agencies and coalition partners to ensure coordinated defense and real-time threat sharing. Standards and Compliance Frameworks Defense cybersecurity must comply with strict regulations and frameworks to ensure security, interoperability, and accountability. Common frameworks include: NIST 800-53: Security and privacy controls for federal information systems. RMF (Risk Management Framework): Used for system accreditation in U.S. defense systems. ISO/IEC 27001: International standard for information security management. STIGs (Security Technical Implementation Guides): Published by DISA to enforce configuration baselines. Emerging Technologies in Military Cybersecurity To stay ahead of advanced threats, defense cybersecurity solutions are evolving rapidly. Key technological trends include: Artificial Intelligence and Machine Learning AI enables real-time pattern recognition, anomaly detection, and automated response to cyber threats. ML algorithms continuously adapt to new attack vectors and behaviors. Zero Trust Architecture This model assumes no implicit trust, verifying every user and device at every step. It reduces the risk of lateral movement within networks after a breach. Post-Quantum Cryptography With the rise of quantum computing, new encryption standards are being developed to protect defense communications from future quantum-based attacks. Blockchain for Data Integrity Blockchain technology offers tamper-proof data storage and secure transaction logging for military supply chains and system logs. Cyber Range and Simulation Virtual environments used to train cyber defense teams and test responses to simulated attacks in a safe, controlled setting.







